To detect something “abnormal” in your computer network, you need to first know how the “normal” looks like … sounds simple, right? do you have a list of the processes that “normally” runs on your computer? network connections? how about system drivers? no? where’s “explorer.exe” in your computer? c:\windows or c:\windows\system32? don’t know? didn’t think so 🙂 so when a “previously-unknown-malware” spews on your windows machine you won’t know … to do that you need a baseline that you can refer to when you compare between what you found and what is … well, “normal”.
Creating baselines of a computer usually comprises collecting information about the following from a “known-clean-state”:
- Running processes.
- Network communications “established and listening”.
- Registry “windows” and startup entries.
- Files.
- Services.
- Loaded modules “DLLs”.
- Drivers.
- installed applications.
- … and few other “users, context …etc.”
Once you have a list of the above stored somewhere in an easy to parse format, you can come later and collect same information then compare the new findings and detect “anomalies”.
Even though for different purposes, the interesting thing is that almost the same list of information is gathered during digital investigations of systems that are running and might have been compromised, some call that process “digital forensic evidence gathering from live systems”.
Microsoft was kind enough to create a tool called `COFEE` that makes gathering this information easier:
wikipedia: Computer Online Forensic Evidence Extractor (COFEE) is a tool kit, developed by Microsoft, to help computer forensic investigators extract evidence from a Windows computer. Installed on a USB flash drive or other external disk drive, it acts as an automated forensic tool during a live analysis. Microsoft provides COFEE devices and online technical support free to law enforcement agencies.
Law enforcement agencies?! What about mere mortals?
COPP – COFEE Of Poor People
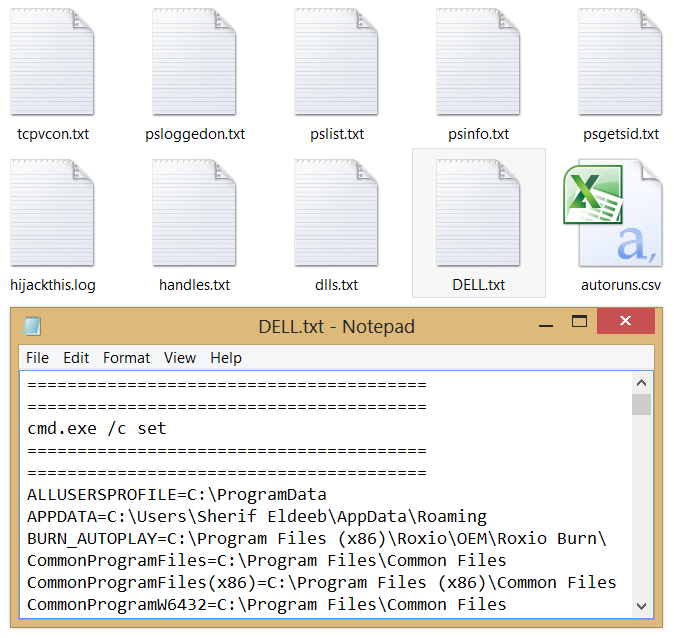
I have been gathering information from computers in an environment as a step to create the above mentioned “baseline”, I often gather information on investigations that involves live systems, so I created a simple DOS batch script to gather the AM information, it’s poor-man’s-effort COFEE.
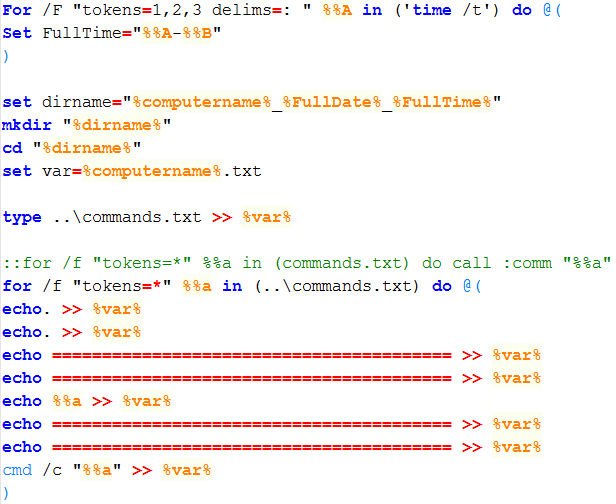
- once executed, it creates a directory “folder” with computer name, time and date, then iterates through a list of commands then pipe the output to a file.
- Run as administrator!
- It can be easily configured to write the output to a windows share instead of local directory, then executed on all machines in a domain environment using a group policy or PsExec “you will also need to adjust how the output is written to the file”.
Get the zip file from here: https://github.com/SherifEldeeb/COPP
NOTE:
If you reached here, this means you really are interested about the topic, please note that a much better way to do that with more comprehensive data is through Mandiant’s Redline, it’s free and straight forward, and that is what I *really* use 😉
Thx Dr , for that information 🙂