
Even though this post is focusing on finding flame malware files in a windows domain environment, the concepts are valid for looking for “any” particular file in your domain machines.
- If you do not know what’s flame, look here.
- A list of flame Command and Control servers (DNS & IPs) can be found here.
In this post, we will be looking for the existence of Flame malware files on every single machine in an active directory using windows’ built in tools (+PsExec).
Introduction
What is Indicators of Compromise (IOC)?
It is a description of technical characteristics that identify a known threat, an attacker’s methodology, or other evidence of compromise, This usually includes artifacts left by an intrusion by looking for the following:
- Network connection attempts to Command and Control Servers.
- Malware Files (DLL, EXE…etc.)
- Registry Keys
- Running Processes
I’m in the Middle East, and we are worried that any of our machines has been (is still) infected with the Flame malware, and we wanted a quick way to check them all in one shot.
IOC – Malware files
Flame has a specific set of files that will get created on Infected machines, one notable file is “~DEB93D.tmp” which is left behind even after malware’s removal, finding this particular file is an indication of previous infection.
The list of flame files that we will be looking for:
~a29.tmp ~d43a37b.tmp ~DEB83C.tmp ~DEB93D.tmp ~DF05AC8.tmp ~dfc855.tmp ~DFD85D3.tmp ~DFL983.tmp ~dra52.tmp ~dra53.tmp ~f28.tmp ~HLV ~HLV084.tmp ~HLV294.tmp ~KWI ~nms534 ~rcj0 ~ZLM0D1.ocx ~ZLM0D2.ocx 00004069.exe 00004784.dll 00005729.dll 00006411.dll advnetcfg.ocx boot32drv.sys ccalc32.sys cmutlcfg.ocx commgr32 contents.btr dcomm.dat desc.ini dmmsapi.dat dsmgr.ocx Ef_trace.log fib32.bat gppref32.exe guninst32 inje kbdinai lib.ocx lmcache.dat lss.ocx m4aaux.dat mprhlp mscrypt.dat msglu32.ocx mssecmgr.ocx ntcache.dat nteps32 nteps32.ocx Pcldrvx.ocx preg.exe rccache.dat SeCEdit soapr32.ocx sstab stamn32 To691.tmp urpd.ocx wavesup3.drv wlndh32 wrm3f0 zff042
I saved them in a file called Flame_File_List.txt
Looking for a particular file (on a local machine)…
Before we dive into how to do it all over the domain, let’s try it on a local machine first… how about looking for “~DEB93D.tmp” in the local machine?: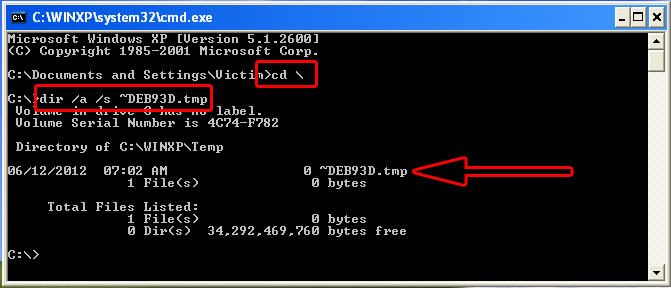
- Run -> cmd.exe
- We change directory to the root “cd \”
- dir /a /s -> /a means list all files, even system and hidden & /s means look in subdirectories.
- Specify the filename you are looking for “~DEB93D.tmp”.
As we can see, a file was found…
Looking for a LIST of files (on a local machine)…
To look for all the files we’re interested in, save them in a file “Flame_File_List.txt”, then we’ll need a DOS Batch file to iterate through them, one by one.
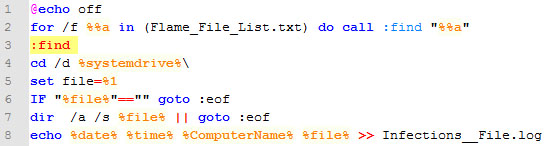
The batch file’s function is clear “idea taken from here“, the only trick is at line 7…
- If *no* files are found, “dir” returns “I am not successful”
- The “||” means `in case the dir command failed, execute the goto instruction, but if the dir command succeeded, do not execute the goto instruction, just move to the next line”.
- So, if “dir” failed, it will go to end of file (i.e. process next entry in the file list and WILL NOT execute the echo command)
- BUT, if a file is found, then the batch file will output the time, date, computer name and the found malware file to a file called “Infections__File.log”
Now, put both files “the .bat and the filelist.txt” in the same directory, then run as admin…
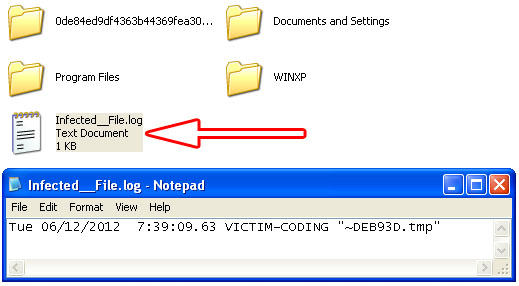
Once it is done, a file that contains all found file is created in your c:\
Executing the BATCH script on *a* remote machine (using PsExec)…
Psexec gives us the option to (copy and run) our batch script on a remote machine, but the thing is that our batch looks for “Flame_File_List.txt” which cannot be copied alongside the .bat file, so, to accomplish that the steps will be as follows:
- Create an everyone-accessible network share on the investigation machine “\\investigation\flame\”
- Copy the “Flame_File_list.txt” to that network share.
- Adjust the batch file to be like the image
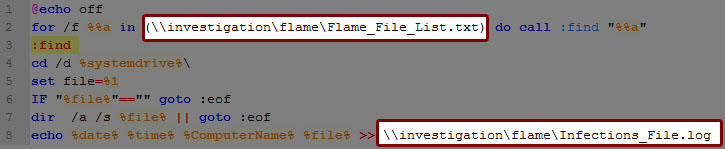
Now we can execute this batch on remote machines without the need to copy it on a thumbdrive and going to each machine…
<code>psexec \\RemoteMachine -u domain\domainadmin -c Flame_LookForFile.bat</code>
Executing the BATCH script on all the machines (using PsExec)…
Psexec also gives us the option to execute the commands on a list of computers in a file, that file format will be “one computer name or IP per line, NO “\\” AT THE BEGINNING”, you can populate that list using “dsquery -computer” or “net view” or any other way you find appropriate, the file has to look like this
- computer1
- computer2
- IP
- IP
- ……
Then save that file as “DomainComputers.txt”, and run PsExec as follows:
<code>psexec @DomainComputers.txt -d -u domain\domainadmin -c Flame_LookForFile.bat</code>
That extra “-d” will make PsExec NOT wait for the batch file to finish before moving to the next computer, it will fire the batch file at all machines AT ONCE….. then go grab a cup of coffee till all the computers in your environment look for the malware files for you and report back if anything was found.
In the next part we will look for running processes using the same concepts.
ATTACHMENTS
Flame_IP_List Flame_LookForFile.bat Flame_File_ListFlame_DNS_List
Nice one mate, keep up the good work.
It would be nice if you have a good source for a deep technical review on Flame , including the features within.
thanks